Linux Capabilities
- 18.7 - Insecure System Components
- https://man7.org/linux/man-pages/man7/capabilities.7.html
- https://book.hacktricks.xyz/linux-hardening/privilege-escalation/linux-capabilities
- https://stackoverflow.com/questions/35469038/how-to-find-out-what-linux-capabilities-a-process-requires-to-work
What are Capabilities in Linux?
Other than the basic file system permission of RWX, linux offers a set of fine-grained permissions that allow processes to do specific tasks with higher privileges (root).
User, group, everyone else (user leo, group leo respectively identified)

Specifically, while traditional UNIX systems distinguish only between 2 process types:
- those privileges (euid = 0)
- those unprivileges (euid != 0)
From linux kernel 2.2 onwards, privileges are split into distinct units known as capabilities which can be enabled of disabled (per-thread attribute).
Capabilities are used to implement the least privilege design principle.
There are 5 capability sets:
- Inherited
- Effective
- Permitted
- Bounding
- Ambient
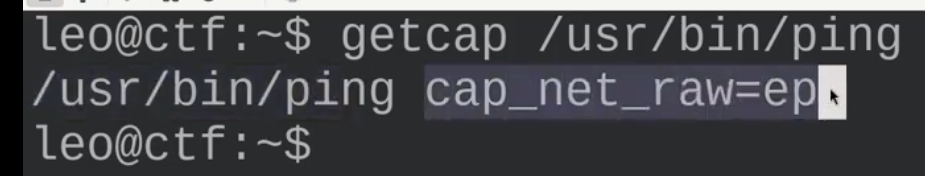
Ping
Ping tends to have the cap_net_raw capability set. This is required to access raw sockets that ping needs to function correctly.
Enumeration
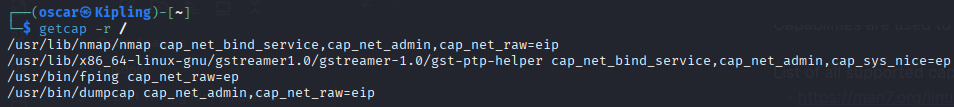
List all binaries with capabilities
getcap -r / 2>&/dev/null
List a specific binaries' capability
getcap /usr/bin/ping
Get the given capabilities of a process given its PID using getpcaps
getpcaps <PID>
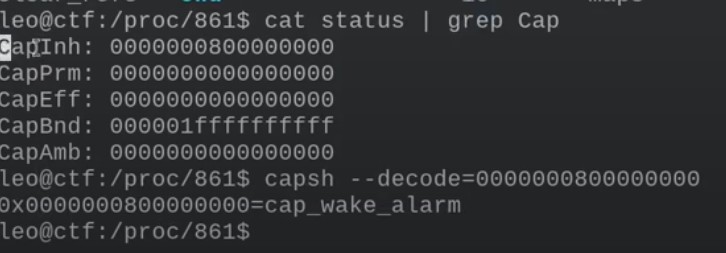
You can also use the pseudo-fs /proc (proc is where running processes are stored)
cat /proc/<PID>/status | grep Cap
Decode the value using capsh to get the capability in plaintext
capsh --decode=000000000000
Creating a new capability
Getcap allows for setting, adding and removing capabilities.
To set a new capability, use the setcap command
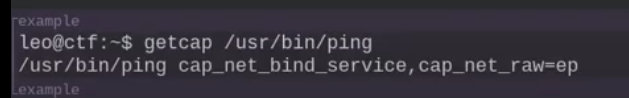
sudo setcap 'cap_net_bind_service=ep cap_net_raw=ep' /usr/bin/ping
With this, we've added the new capability cap_net_bind_service
Remove a capability with setcap but using the minus sign
sudo setcap 'cap_net_bind_service=ep cap_net_raw=ep' /usr/bin/ping
Exploitation
Some capabilities can be used for privilege escalation.
Check 18.7 - Insecure System Components for more in-depth common vulnerabilities.
Some interesting capabilities that can be used for exploitation include:
CAP_SYS_ADMIN
- Allows extensive administrative privileges, such as mounting devices.
CAP_SYS_PTRACE
- Allows to use debugging and system call tracing functionalities (ptrace).
CAP_SYS_MODULE
- Allows to load and unload kernel modules. A lot of rootkits start off as kernel modules, that hide and modify data structures from within the kernel.
CAP_SETUID
- Allows to set the effective user id of the created process.
Other interesting capabilities include:
- CAP_DAC_READ_SEARCH
- CAP_DAC_OVERRIDE
- CAP_CHOWN
- CAP_FOWNER
- CAP_SETGID
- CAP_SETFCAP
- CAP_SYS_RAWIO
- CAP_KILL
- CAP_NET_BIND_SERVICE
- CAP_NET_RAW
- CAP_LINUX_IMMUTABLE
- CAP_SYS_CHROOT
- CAP_SYS_BOOT
- CAP_SYSLOG
- CAP_MKNOD
- CAP_SETPCAP